Welcome to part one of our two-part deep dive into Mimecast's Human Risk Command Center (HRCC). In this first installment, we'll explore what the Command Center is and how it operates from a workflow perspective. Part two will focus exclusively on adaptive policies—examining how these intelligent controls automatically adjust security measures based on user behavior and organizational threats.
What is the Human Risk Command Center?
The HRCC serves as your central Human Risk Management solution. Rather than treating all users equally, the HRCC recognizes that different employees present varying levels of vulnerability. The Human Risk management (HRM) platform works together to create a comprehensive ecosystem:
- Advanced Risk Scoring transforms abstract human behavior into quantifiable metrics. The system assigns dynamic risk scores on a 0-10 scale to individual users based on their email interactions, phishing simulation performance and awareness training completion, and sensitive data handling events.
- Integrated Security Intelligence aggregates data from multiple sources such as malware interaction from EDR providers, sensitive data handling from DLP solutions, identity attacks from IAM solutions and phishing simulation tools. This comprehensive data collection enables the Human Risk Command Center to build detailed risk profiles that reflect real-world user behavior patterns.
- Proactive Interventions When risky behavior is detected, the HRM platform informs Mimecast Engage* (*requires a Mimecast Engage license) to deliver just-in-time behavioral corrections and personalized training modules.
- Adaptive Policies represent the HRM platform's ability to automatically adjust security controls based on user risk profiles. Instead of applying blanket policies across all users, HRCC enables targeted interventions that scale protection levels according to individual risk assessments. Actions can be applied in email security and Incydr* (*requires an Incydr license)
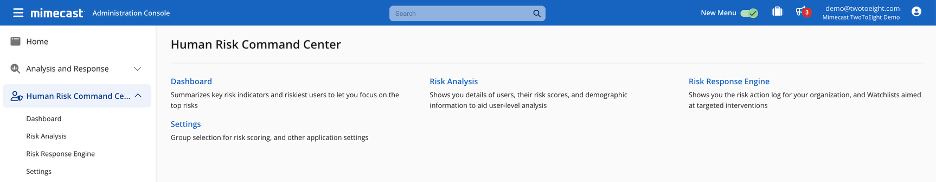
How the Human Risk Command Center Works
It operates through six interconnected phases that create a continuous cycle of risk assessment and response.
Phase 1: Data Collection The HRM platform continuously aggregates behavioral data from multiple touch points across your security ecosystem. This includes phishing simulation results that reveal user susceptibility patterns, sensitive data handling events that indicate data loss risks, malware interaction logs, and identity risk indicators.
Phase 2: Real-Time Risk Assessment The collected data feeds into sophisticated algorithms that calculate dynamic risk scores for each user. Unlike static risk assessments, these scores update in real-time as new behavioral data becomes available. The HRCC weighs multiple factors to create a holistic risk profile.
Phase 3: Risk Classification As events are received, the HRCC compares user risk scores against established thresholds. Users with high risk scores automatically receive ‘Very High’ classification. This regular reassessment ensures that risk classifications remain current with evolving user behavior patterns.
Phase 4: Profile Group Assignment The HRM platform automatically creates and maintains two specialized profile groups that enable organizations to implement adaptive security responses based on real user behavior. Every six hours, the Human Risk Command Center evaluates all user risk scores and identifies high risk and highly attacked users, updating these classifications to ensure current risk intelligence drives security decisions. It's important to note that administrators cannot manage these groups
Phase 5: Intervention Delivery When behavioral triggers indicate risky actions, the HRCC deploys targeted interventions through Mimecast Engage. These consist of Slack, Microsoft Teams or email notifications with personalized security reminders, or enrollment in additional training modules.
Phase 6: Policy Enforcement Profile group assignments trigger automatic policy adjustments across the Mimecast platform. High-risk users might receive stricter email filtering, removal of attachment editing through Safe File Conversion, or increased BEC scanning. Mimecast and Incydr can be integrated to synchronize user profile groups and watch lists, ensuring that high-risk users identified in one platform are automatically reflected in the other.
The Human Risk Management Profile Groups
The HRM platform automatically creates two profile groups for assigning your organization's most vulnerable users:
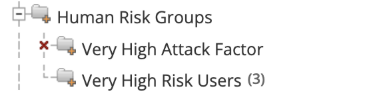
Very High-Risk Users: Behavioral Intelligence in Action
The Very High-Risk Users group captures individuals whose demonstrated behaviors indicate elevated vulnerability. Users automatically join this group when their risk score reaches or exceeds 8.0 based on the:
- Clicking phishing links
- Misidentifying phishing simulations
- Interacting with malware
- Awareness training completion metrics
- Sensitive data mishandling
The scoring methodology weighs each data source according to its predictive value for future security incidents. Critical activities, such as phishing clicks, can dramatically increase a user's risk score within a single measurement cycle.
A user's risk level decreases over time based on sustained positive cybersecurity behaviors, typically following a linear decay rate that will return a user with a score of 10 in a behavior to 0 in approximately one year.
Very High Attacked Factor: Threat-Centric Classification
The Very High Attack Factor Users group identifies employees who face disproportionate targeting from external threats compared to their peers in the organization. These users receive a "Very High" Attack Factor rating based on the volume of attacks directed specifically at them. Users automatically join this group when their attack factor reaches or exceeds 8.0 based on:
- Volume of identified email threats
- Identity-based threats - impossible login attempts and brute force attacks.
A user’s attack factor score is based on the past 30 days of attacks.
How to Get Started
To begin using the HRCC, access it through the Mimecast Administration Console. Once logged in, Human Risk appears in the left navigation area.
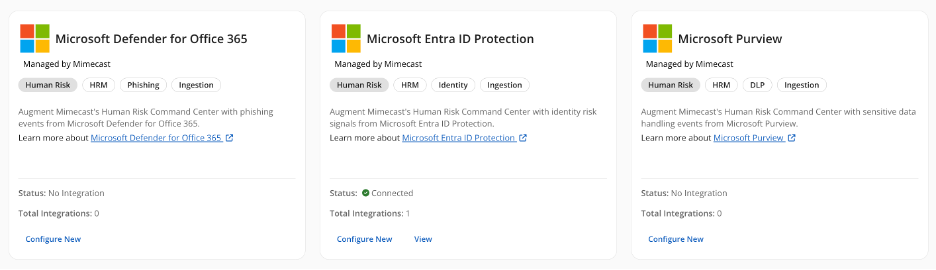
Setting Up Integrations for Comprehensive Risk Visibility
Enable Integrations: Identify which risk types are most relevant to your organization and should factor into risk scores across your user base through integrations with your existing security infrastructure. Browse to the integration hub to get started
Key Integration Categories:
- Endpoint Detection and Response (EDR) providers for malware interaction
- Data Loss Prevention (DLP) solutions for sensitive data handling
- Identity and Access Management (IAM) platforms for identity-based risk events
- Email Security tools for phishing clicks
- Security Awareness Training platforms for phishing simulation and training
Scoring Group: You will be prompted to select a risk scoring group. The scoring group to be used can either be the pre-determined default group or a group you can specify.
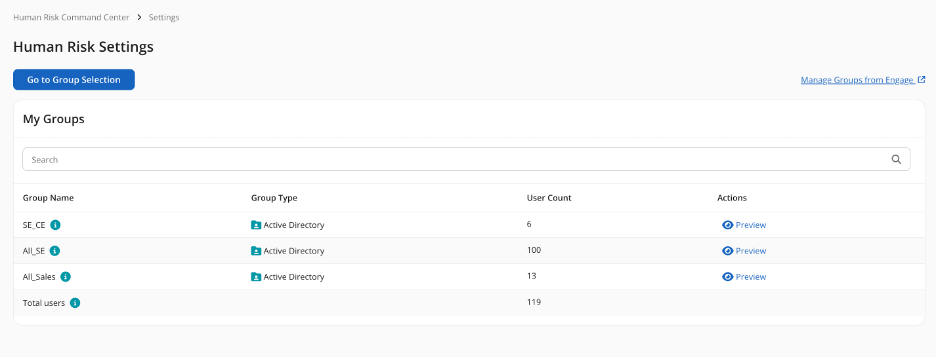
Monitor Automated Profile Groups: Begin monitoring the automatically generated "Very High-Risk Users" and "Very High Attack Factor" groups as they populate based on real user behavior and threat patterns.
For detailed information about available integrations and setup procedures consult the resources available through Mimecast's community links below.

Next Up: In part two of this series, we'll dive deep into adaptive policies—exploring how these intelligent controls automatically adjust security measures based on user behavior, threat context, and organizational requirements.
Knowledge Base Articles
Human Risk Command Center Overview
Human Risk Integrations (Also previously called Engage integrations)
List of available Human Risk Integrations (filter by HRM Platform)