The Multi-Vector Threat Reality
A successful phishing campaign targeting your employees doesn't end when malicious content reaches an inbox. It extends to endpoint compromise, lateral movement, and data exfiltration. Yet most organizations find themselves managing these interconnected threats through isolated security tools, creating response delays that can determine whether an incident becomes a contained event or a catastrophic breach.
While email security and endpoint protection have evolved into powerful platforms, they typically operate in isolation, lacking the intelligence sharing and coordinated response capabilities needed to address modern, multi-vector attacks. This disconnect creates critical blind spots that threat actors actively exploit, moving seamlessly between email and endpoint vectors while security teams struggle to correlate activities across separate tools.
Integration Overview
The Microsoft Defender threat sharing integration transforms this fragmented approach by enabling seamless, bi-directional communication between Mimecast's email security platform and Microsoft Defender for Endpoint. This integration creates an automated bridge that allows near real-time sharing of threat intelligence, including malicious file hashes, URLs, and sending domains, between both platforms. The value that the integration provides to you is:
Enhanced Security Posture
The integration delivers improved threat detection and mitigation capabilities across both email and endpoint.
Accelerated Threat Response
Traditional security operations often involve manual correlation when threats move between email and endpoints. The integration reduces this threat dwell time through automated intelligence sharing.
Streamlined Security Operations
Security teams eliminate the need to manually correlate threat data between separate platforms. This unified approach reduces administrative overhead and minimizes the risk of human error during incident response.
How the Integration Works
Consider an attack that begins with a phishing email containing a malicious attachment. Here's how the integrated platforms coordinate to stop the threat:
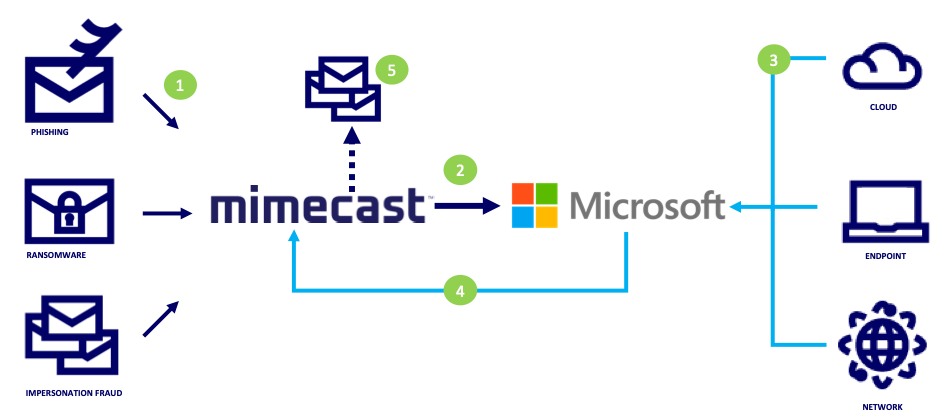
1. Initial Detection and Analysis - Mimecast's AI-driven detection engines identify the suspicious email during analysis, recognizing advanced malware, suspicious sender domains, or weaponized URLs embedded within the message. The email is quarantined while extracting threat indicators for intelligence sharing.
2. Rapid Intelligence Distribution - Within minutes of detection, Mimecast automatically initiates secure API calls to share the identified threat indicators with Microsoft Defender for Endpoint. This includes specific file hashes, malicious URLs, and sender domains that pose risks to organizational endpoints.
3. Coordinated Endpoint Protection - Microsoft Defender immediately incorporates this threat intelligence into its endpoint protection policies, updating threat signatures and behavioral detection rules across all managed devices. If any user attempts to access the same malicious URL or download a file with the flagged hash, Defender blocks the action instantly and generates an alert for security teams.
The bi-directional nature of this integration proves equally powerful when threats originate from endpoint activity. Consider this scenario:
3. User Endpoint Interaction - An employee downloads what appears to be a legitimate software update from a compromised website. Microsoft Defender for Endpoint immediately recognizes the file as malicious based on its behavioral analysis and file signature, blocking execution and quarantining the threat.
4. Immediate Intelligence Sharing - Microsoft Defender extracts the threat indicators—including the malicious file hash, the compromised domain hosting the download, and any associated URLs—and shares this intelligence with Mimecast within minutes. This automated sharing ensures that email security systems gain immediate awareness of the endpoint-detected threat.
5. Proactive Email Scanning and Protection - Mimecast receives these threat indicators and immediately initiates comprehensive scanning across mailboxes and searches for any emails containing references to the compromised domain, links to the malicious download, or attachments. When Mimecast identifies emails containing these threats, it automatically removes them from user inboxes and blocks future delivery attempts.
When each platform ingests threat indicators from the other, administrators gain flexible response capabilities:
Microsoft Defender Options:
- Automatic blocking of flagged URLs, domains, and file hashes across all endpoints
- Quarantine of detected threats with optional user notification
- Custom alert generation for security team investigation
- Integration with existing security orchestration and automated response workflows
Mimecast Options:
- Immediate email quarantine and removal from user inboxes
- Proactive scanning of email archives for historical threat presence
- Automatic blocking of future emails containing flagged indicators
- User notification and security awareness training trigger based on threat exposure
Getting Started
Begin the process by accessing the Integration Hub through the Mimecast Administration Console, where you'll first select the fetch duration for historical threat information.
Next, configure threat indicator sharing. Define which indicators Mimecast shares with Microsoft Defender, including malicious file hashes from Attachment Protection, URLs from URL Protection, and domains from Impersonation Protection. For each indicator type, specify the enforcement action Microsoft Defender takes when encountering these threats. Set corresponding alert configurations with severity levels and indicator expiration periods.
Similarly, determine which indicators flow from Microsoft Defender back into Mimecast, including file hashes, URLs that update Managed URLs, and domains that create blocked sender policies. Enable automated remediation capabilities to search existing email for previously delivered threats and remove associated messages when imported indicators match historical content. Configure whether to import indicators from both Microsoft Defender's indicator list and active alerts to maximize threat coverage.
Complete the operational setup by configuring notification recipients for error alerts, ensuring operational teams receive prompt notification if connectivity issues arise. Finalize the integration by authorizing Mimecast's access and granting permissions.
For detailed configuration guidance and troubleshooting support, reference the Knowledge base article.
Mimecast and Microsoft
Mimecast has built a number of integrations eliminating the complexity of managing disparate security tools while maximizing your existing Microsoft investments.
Microsoft Products combines attack simulation data, phishing clicks and malware interaction, identity risk events, and data governance insights into Mimecast's Human Risk Management platform. This enables you to correlate your users behavior delivering comprehensive risk scoring that identifies your most vulnerable employees and automates targeted interventions. This allows security teams to prioritize training, adjust policies, and respond to threats based on actual user risk rather than generic security rules. Explore all available Human Risk Management integrations at
https://integrations.mimecast.com/tech-partners/
(select the product filter to 'HRM Platform')
Microsoft Sentinel Integration ingest Mimecast security events and audit logs, enabling unified security monitoring and targeted incident response using email context. Explore the integration at
https://integrations.mimecast.com/tech-partners/microsoft-sentinel/
.
Power BI Integration enables you to visualize Mimecast threat data within familiar Microsoft analytics dashboards, supporting data-driven security decisions. Learn more at here.
Ready to enhance your organization's threat defense capabilities? Navigate to the Integration Hub to get started.